Current state: Under Discussion
To support authentication by username/password when accessing milvus instance.
There is no basic security model for milvus instances currently. Users can access any milvus instance once they have the address by any milvus sdk.
This project aims to support basic authentication with username/password. Clients need to provide username and password when accessing the milvus instance.
Prerequisite
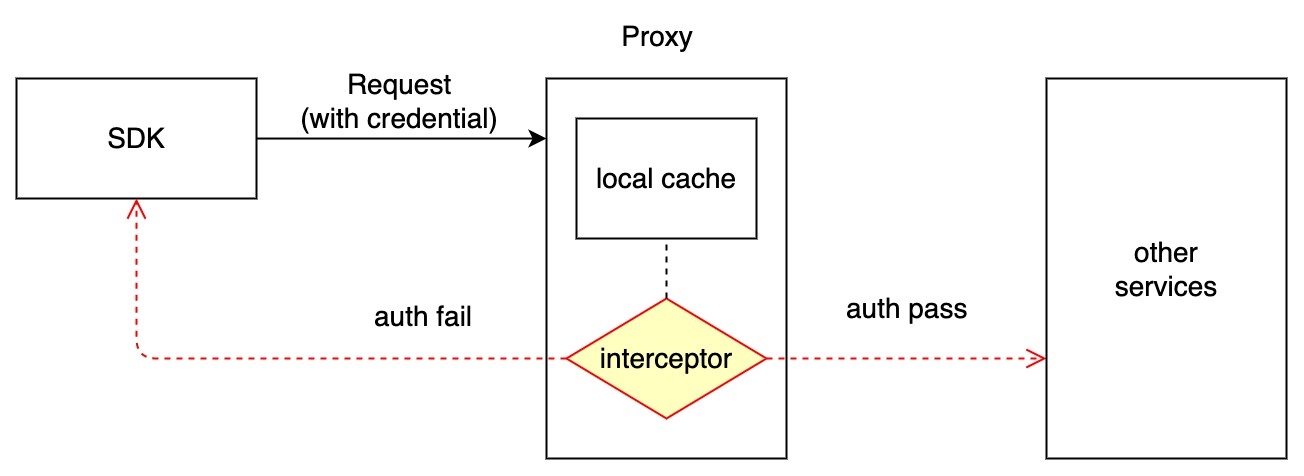
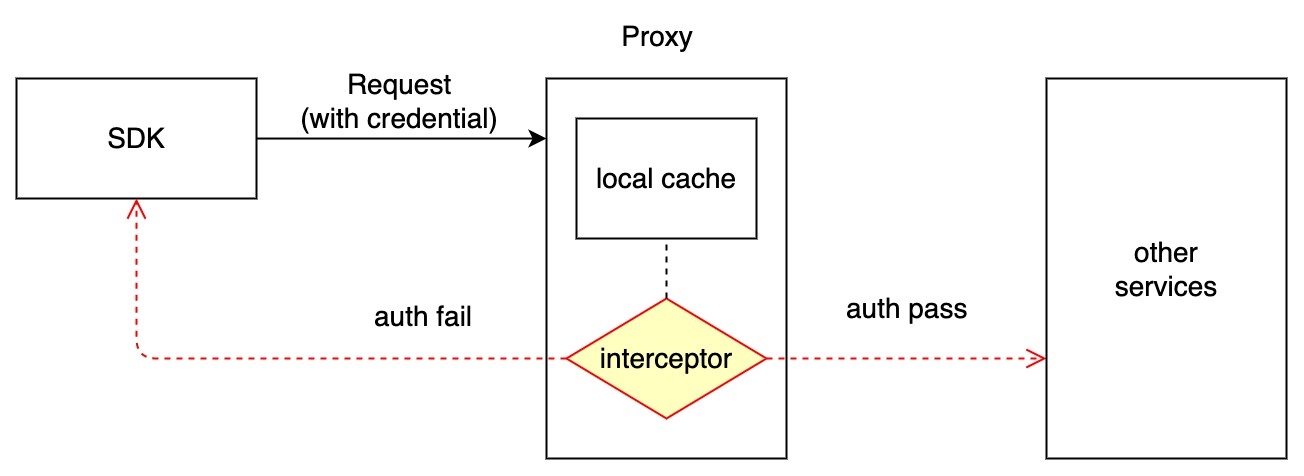
Authentication Workflow
Since grpc requests all handled by proxy, we will do the authentication in the proxy component. Logging in to the milvus instance will follow the processes below:
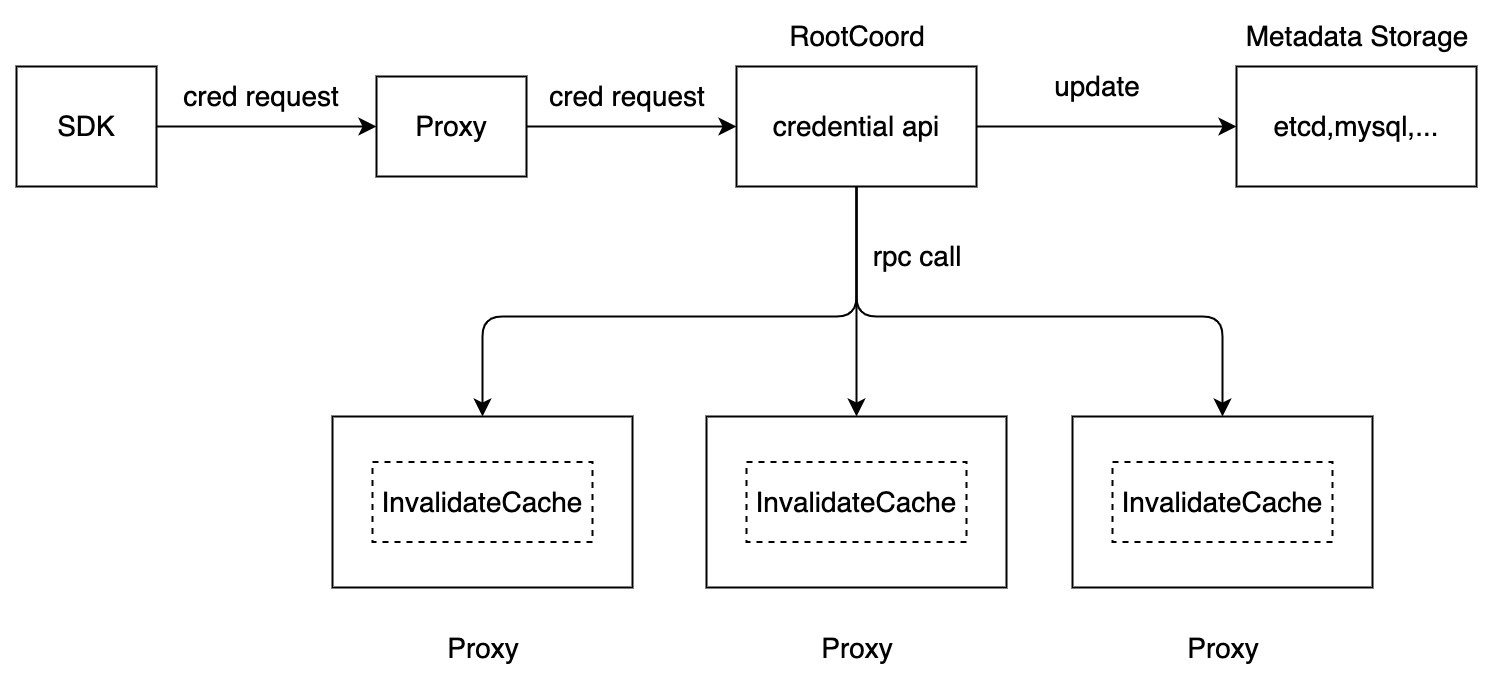
Cache Update Workflow
1、Credential apis are provided by RootCoord.
2、Credential apis persist credentials on etcd (or other storage like mysql), and create task called CredTask for updating local caches in all proxy components.
3、CredTask will iterate all the proxy components, and call every proxy's rpc for updating the local cache until all of them are success.
4、Auth interceptor in proxy component will just search credential records from local cache.
Etcd model for credentials
Key: ${prefix}/credentials/users/${username} Value: {"password": ${encrypted_password}, ...} |
Interface of credentials apis
struct Credential {
username string,
password string
}
func NewCredential(cred Credential) (bool,error)
func ListUsers() []string
func UpdateCredential(cred Credential) (bool,error)
func DeleteCredential(username string) (bool,error) |
Compatibility
To be compatible with preview version, Milvus will detect the records on credentials path in etcd whether users are created for the milvus instance. If there are non users, it acts like the non-authenticate mode. Otherwise it will check the credentials for each grpc call.
Case 1: create credentials for milvus
Case 2: no credentials created for milvus
SSL/TLS transportation
Authorization on RBAC control