Current state: Under Discussion
To support authentication by username/password when accessing milvus instance.
There is no basic security model for milvus instances currently. Users can access any milvus instance once they have the address by any milvus sdk.
This project aims to support basic authentication with username/password. Clients need to provide username and password when accessing the milvus instance.
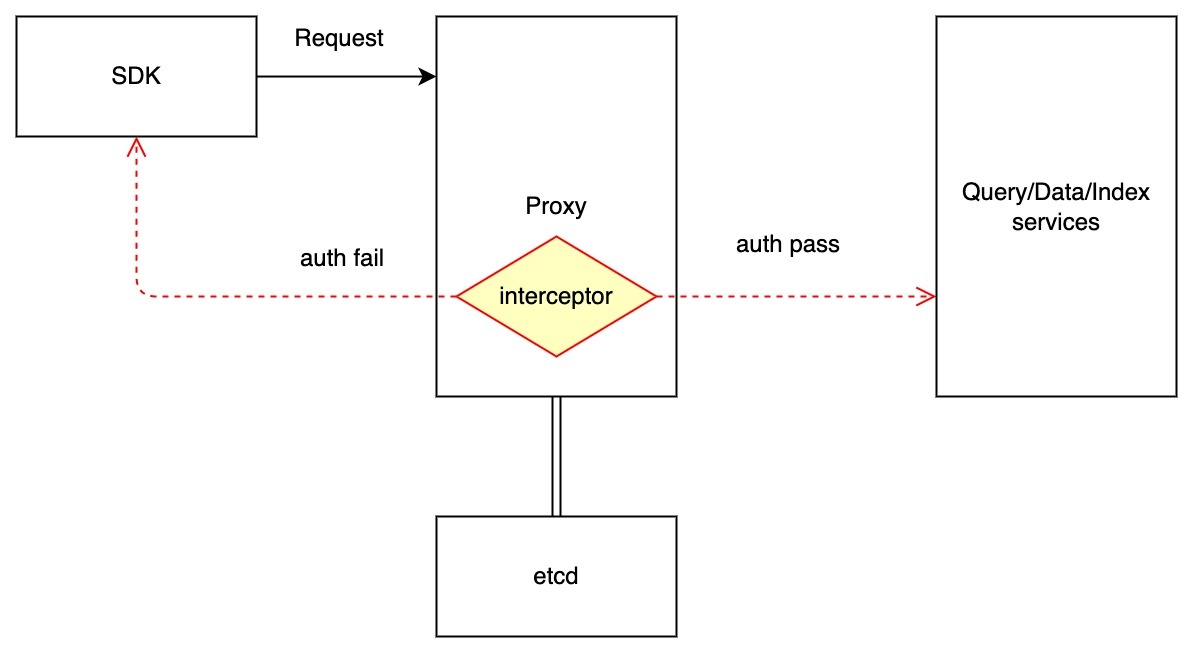
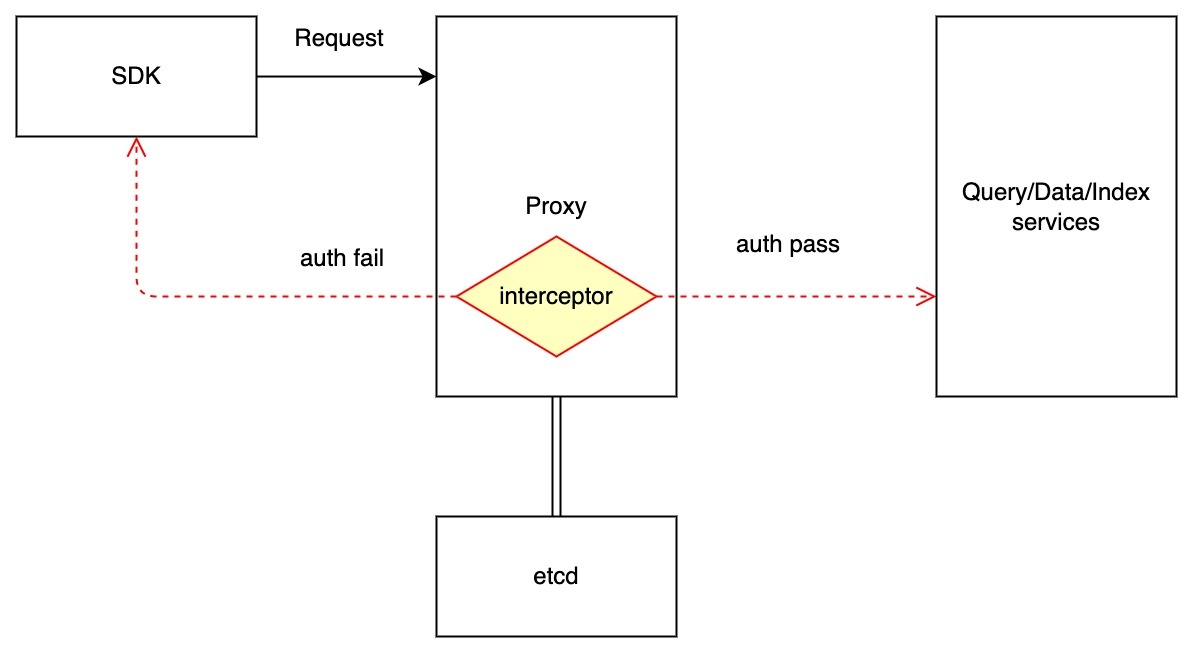
Since grpc requests all handled by proxy, we will do the authentication in the proxy component. Logging in to the milvus instance will follow the processes below:
Etcd model for credentials:
Key: ${prefix}/credentials/users/${username} Value: {"password": ${encrypted_password}, ...} |
Interface for operating credentials:
struct Credential {
username string,
password string
}
func NewCredential() (bool,error)
func ListCredential() []Credential
func GetCredential(username string) *Credential
func UpdateCredential(cred Credential) (bool,error)
func DeleteCredential(username string) (bool,error) |
This project also aims to provide HTTPS transport security, and it takes several certificate related configuration options, either through command-line flags or environment variables:
--cert-file=<path>: Certificate used for SSL/TLS connections to milvus.
--key-file=<path>: Key for the certificate. Must be unencrypted.
--client-cert-auth: When this is set milvus will check all incoming HTTPS requests for a client certificate signed by the trusted CA, requests that don’t supply a valid client certificate will fail.
--trusted-ca-file=<path>: Trusted certificate authority.
--auto-tls: Use automatically generated self-signed certificates for TLS connections with clients.
Case 1: create credentials for milvus
Case 2: no credentials created for milvus
Case 3: https enabled for milvus
Case 4: https not enabled for milvus
Authorization on RBAC control